Solved How could an adversary obtain remote screen access to
Por um escritor misterioso
Descrição
Answer to Solved How could an adversary obtain remote screen access to

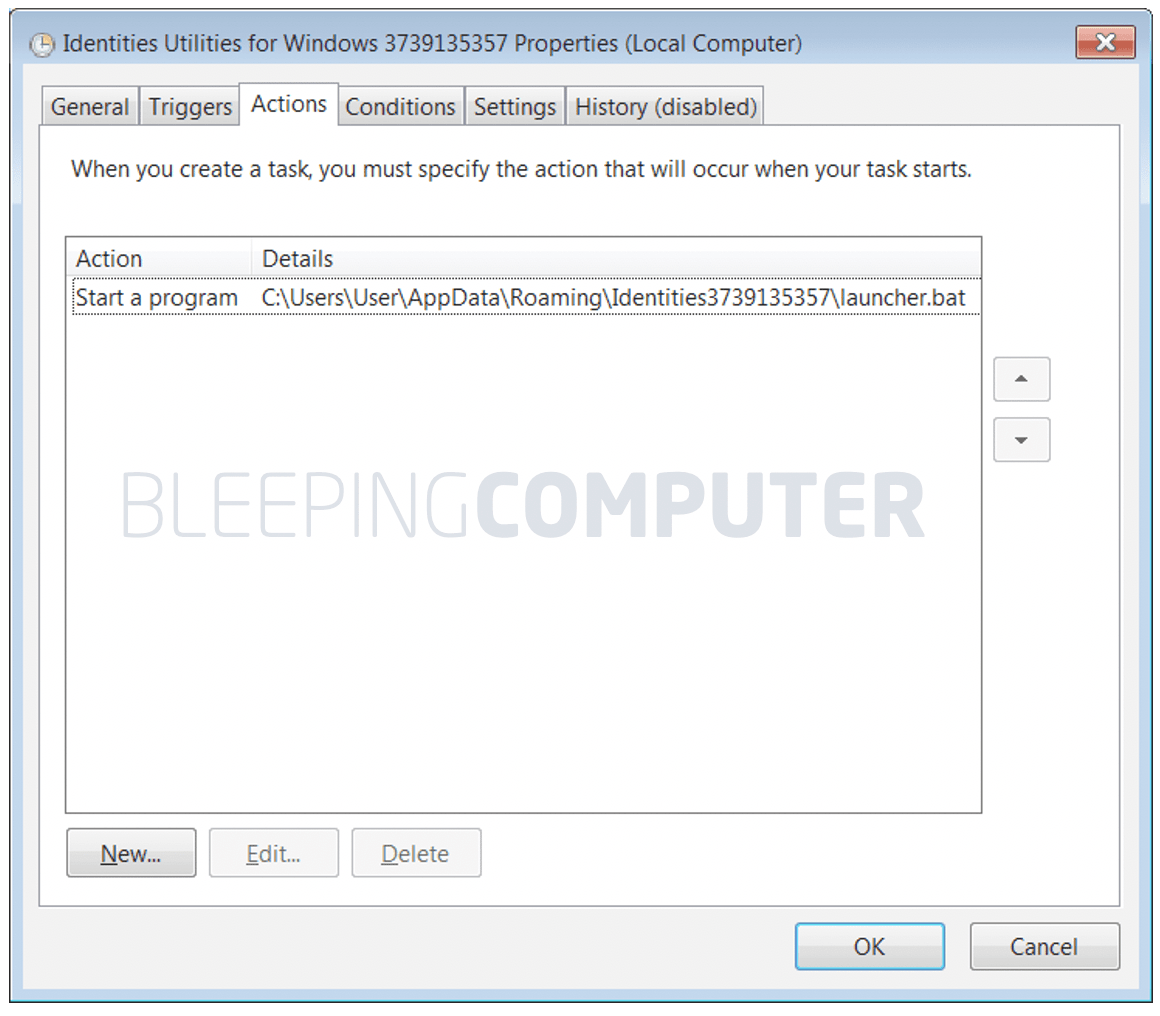
Okta Post-Exploitation Method Exposes User Passwords

At The Crossroads Of Identity: The Relationship Between Remote Work And Ransomware

How to Compromise a Printer in Three Simple Steps

Attacking RDP from Inside: How we abused named pipes for smart-card hijacking, unauthorized file sys
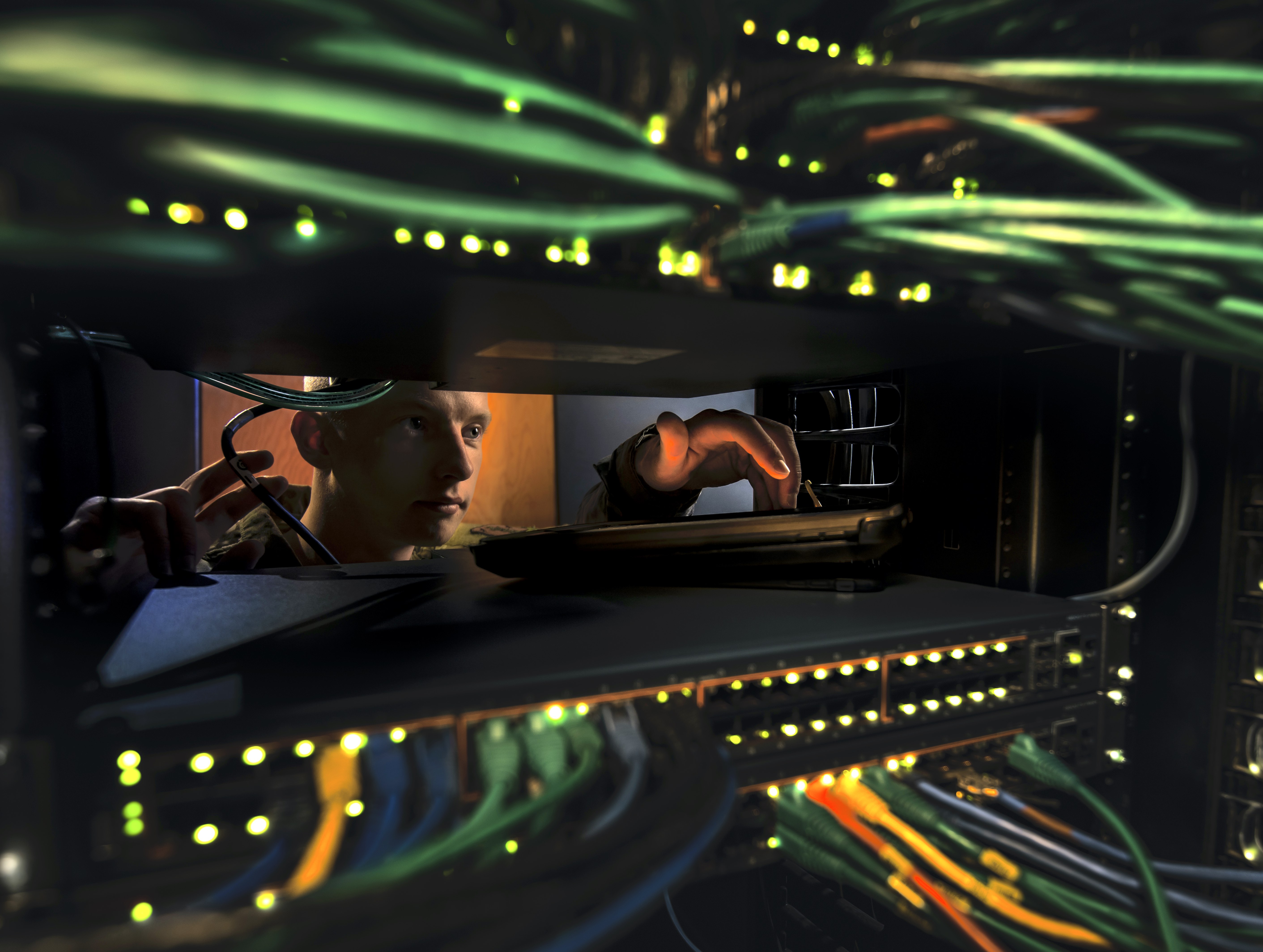
Navy, DoD Networks Strained Under Telework Demand; Leaders Ask 'Limit use of REPLY TO ALL' - USNI News
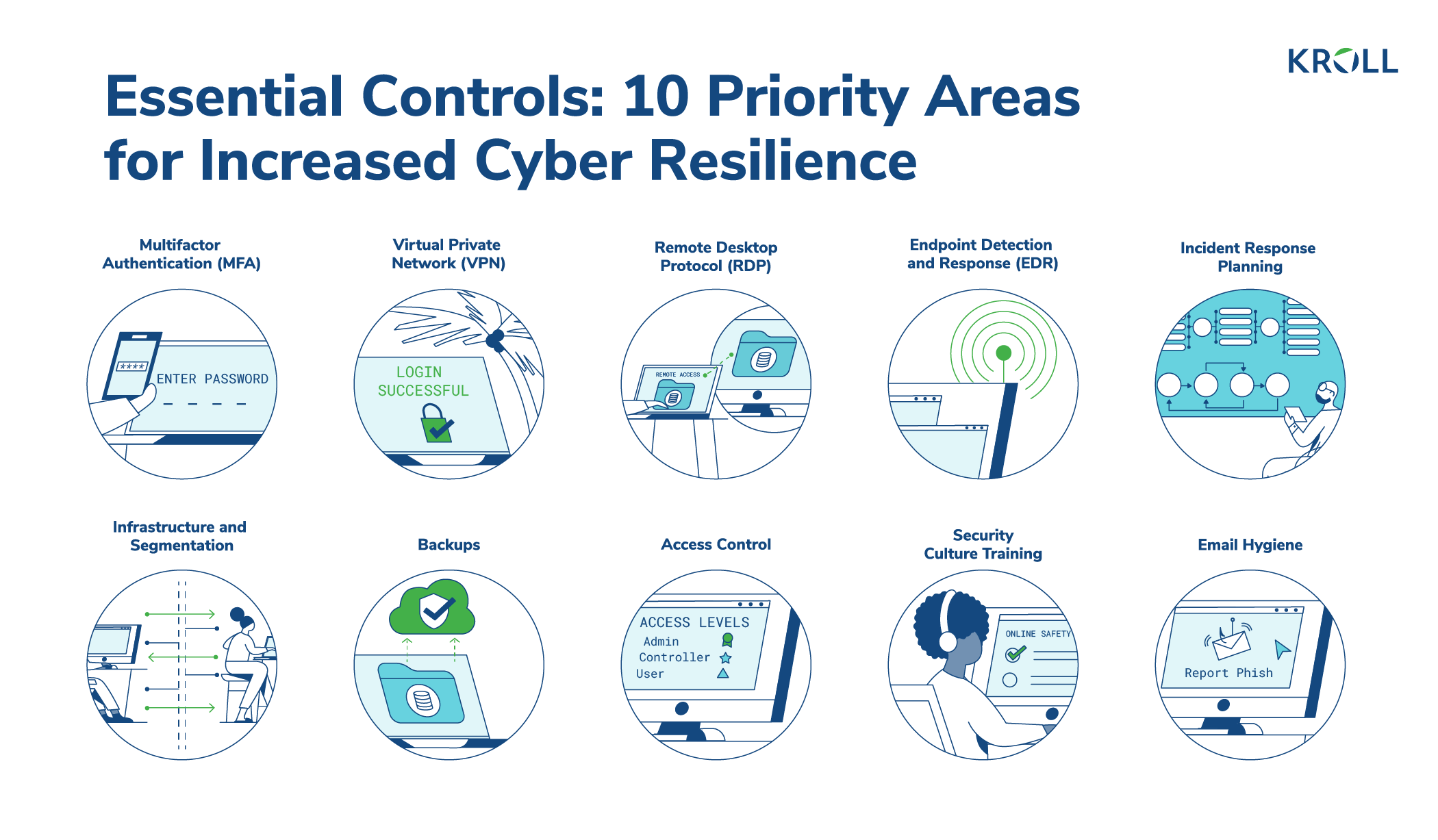
10 Essential Cyber Security Controls for Increased Resilience

The risks of remote desktop security & how to overcome them
What is Endpoint Management? - SentinelOne

RDP Brute Force Attack: Protect Your VDI (Virtual Desktop Infrastructure)

Computer security - Wikipedia
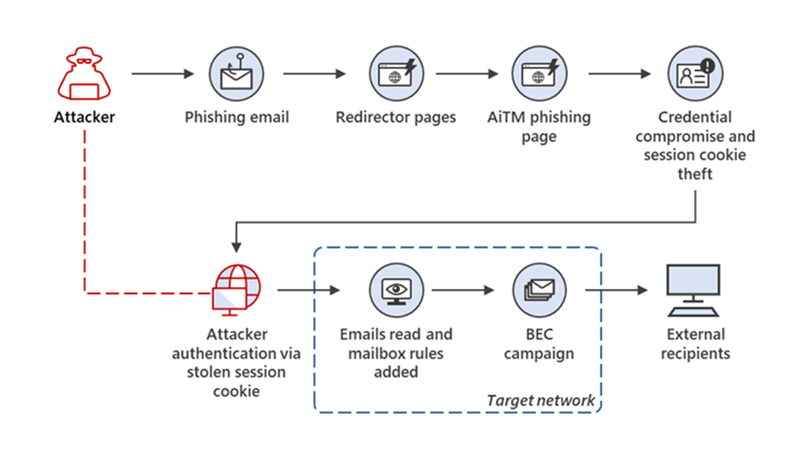
From cookie theft to BEC: Attackers use AiTM phishing sites as entry point to further financial fraud

Identifying malicious Remote Desktop Protocol (RDP) connections with Elastic Security
No More App-Switching. Forget learning to navigate a new screen with every app. TiVo Stream 4K enables one centralized place for searching, browsing,

TiVo Stream 4K – Every Streaming App and Live TV on One Screen – 4K UHD, Dolby Vision HDR and Dolby Atmos Sound – Powered by Android TV – Plug-In
de
por adulto (o preço varia de acordo com o tamanho do grupo)