Cryptographic Keys 101: What They Are & How They Secure Data - Hashed Out by The SSL Store™
Por um escritor misterioso
Descrição
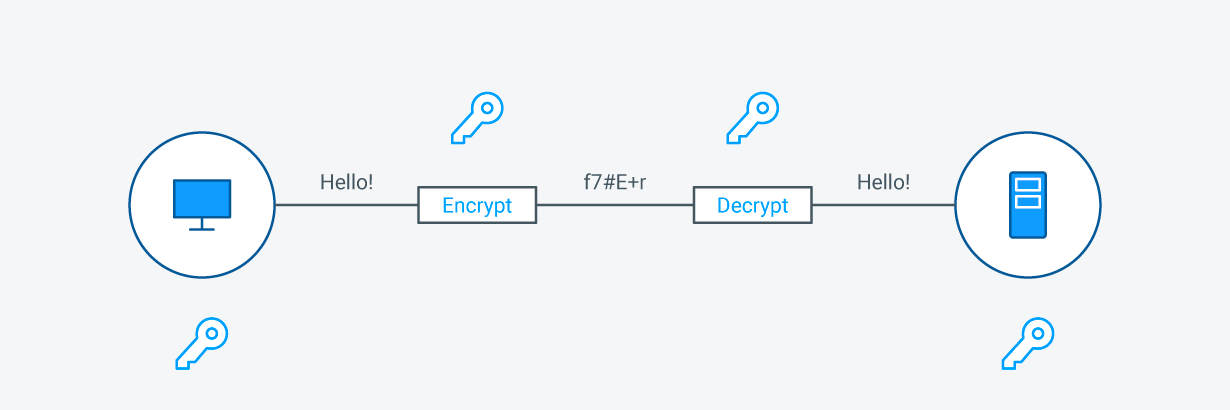
Cryptographic keys, in combination with an encryption algorithm, disguise data (encryption) so only a special key can access it (decryption).

Cryptography 101: Key Principles, Major Types, Use Cases
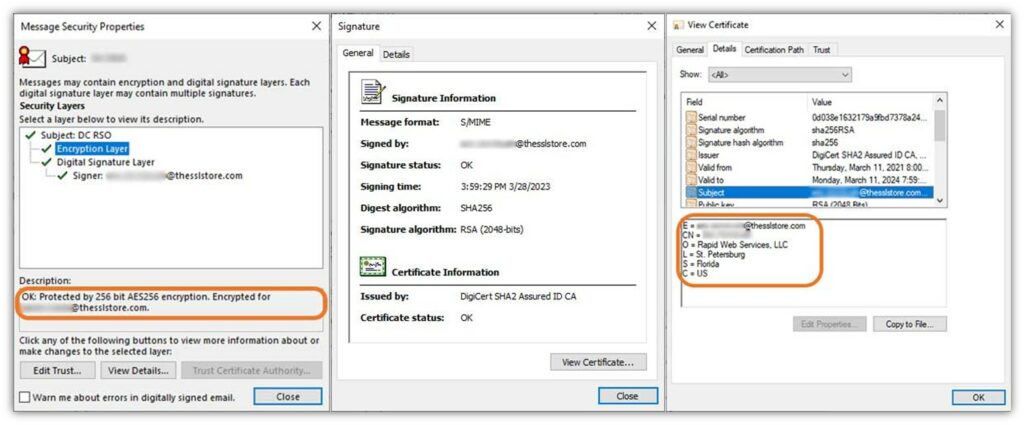
Cryptographic Keys 101: What They Are & How They Secure Data

An Overview of Cryptography

An Overview of Cryptography
What is SSL Cryptography?
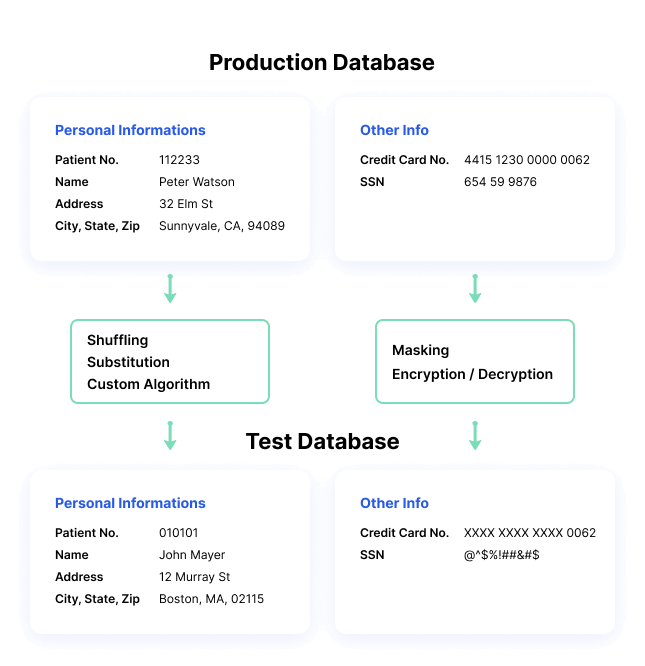
What is Data Masking?, Techniques & Best Practices
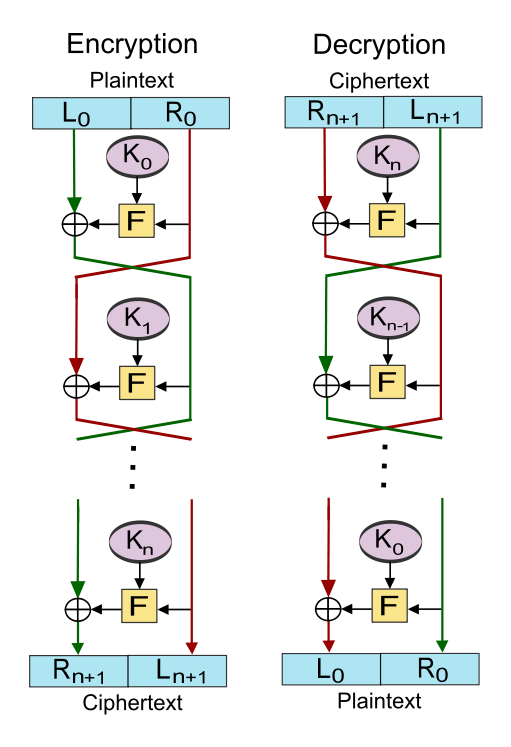
An Overview of Cryptography
The SSL Store: ACME Protocol: What it is and how it works 05/31
Cryptographic Keys 101: What They Are & How They Secure Data
The SSL Store: What Is a Hash Function in Cryptography? A

Cryptographic Hashing: A Beginner's Guide - 101 Blockchains
de
por adulto (o preço varia de acordo com o tamanho do grupo)


:max_bytes(150000):strip_icc()/__opt__aboutcom__coeus__resources__content_migration__mnn__images__2009__12__main_chanie_keys-06c395c828514db7aac45a3dcf64b0eb.jpg)



:quality(90)/cloudfront-us-east-1.images.arcpublishing.com/elcomercio/DZU7VZWCANGHXFRNL6UCYWYIDU.jpg)