PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage
Por um escritor misterioso
Descrição
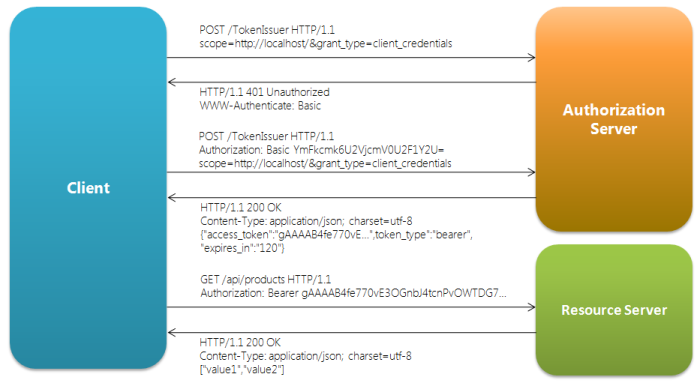
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://miro.medium.com/v2/resize:fit:984/1*yfkIuatmHUAaYYWCdF_IDQ.png)
OAuth Access Token Implementation, by Takahiko Kawasaki
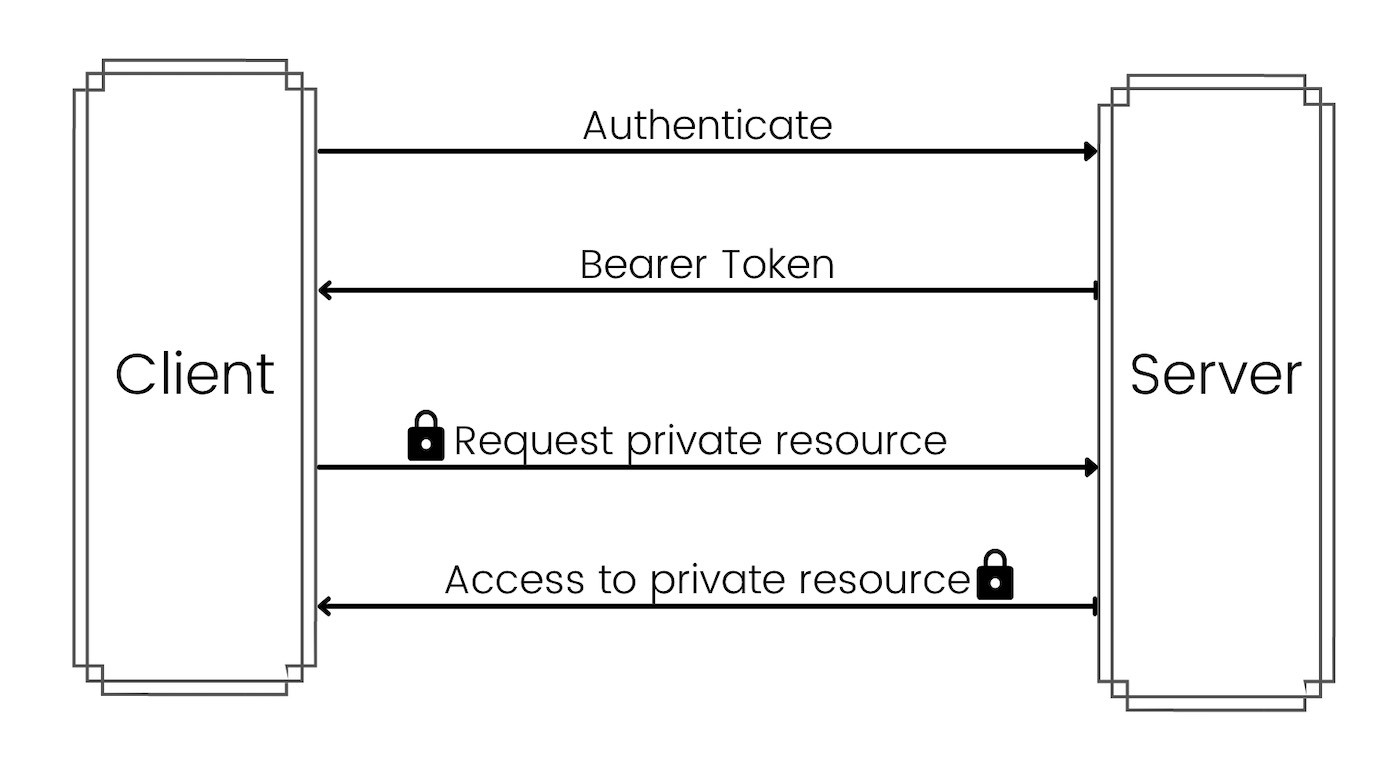
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://developer.orange.com/od-uploads/2-legged-oauth_902px.png)
Introduction to OAuth 2.0 protocol - Orange Developer
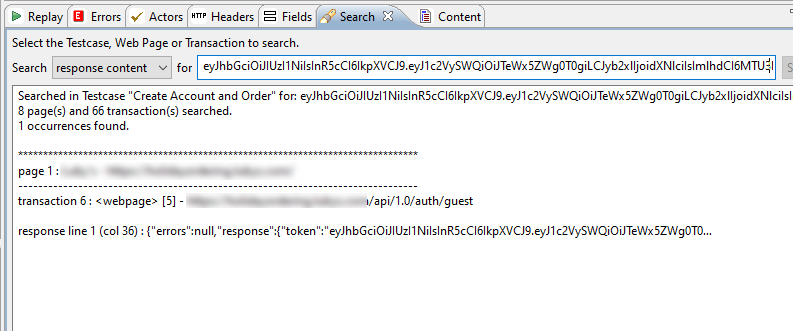
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://media.springernature.com/m685/springer-static/image/art%3A10.1007%2Fs10207-021-00551-w/MediaObjects/10207_2021_551_Fig2_HTML.png)
Machine learning approach to vulnerability detection in OAuth 2.0 authentication and authorization flow
Xero OAuth 2.0 with Ruby. Xero API support for OAuth 2 is now…, by Jenks Guo
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://d3i71xaburhd42.cloudfront.net/d4a10ef40508abc54dfd94b28a562d3bff77c013/4-Figure1-1.png)
Internet Engineering Task Force (ietf) the Oauth 2.0 Authorization Framework: Bearer Token Usage
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://cloudsundial.com/sites/default/files/2021-03/Web%20Server%202600.png)
General OAuth 2.0 Flows
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://www.hitachi.com/rev/archive/2020/r2020_05/05a04/image/fig_02.png)
Authentication and Authorization Based on OSS for Secure System Interoperation : Hitachi Review
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://www.researchgate.net/publication/317936413/figure/fig1/AS:513117629186048@1499348184550/Token-exchange-and-validation-when-a-bearer-b-JWT-and-c-PoP-tokens-are-used.png)
Token exchange and validation, when (a) bearer, (b) JWT, and (c) PoP
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://static1.smartbear.co/soapui/media/images/stories/oauth2/oauth2flow.png)
OAuth2 Overview
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://www.microfocus.com/documentation/single-sign-on/help/single-sign-on-admin/graphics/oauth_20_authorization_a.png)
Understanding OAuth 2.0 - NetIQ Single Sign-on Administration Guide
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://knowledgecenter.zuora.com/@api/deki/files/14993/Third_Party.jpg?revision=1&size=bestfit&width=735)
Configure Third-party Authentication - Zuora
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://pbs.twimg.com/media/F_MrKxwasAAc7Vw.jpg:large)
Bytebytego on X: OAuth 2.0 (Open Authorization) Explained With Simple Terms. OAuth 2.0 is a powerful and secure framework that allows different applications to securely interact with each other on behalf of
![PDF] The OAuth 2.0 Authorization Framework: Bearer Token Usage](https://www.cloud4u.com/upload/medialibrary/fcf/deznzsr72dopc5lq4043x6xyaxyhkxd5/oauth_overview.png)
OAuth 2.0: An Overview
de
por adulto (o preço varia de acordo com o tamanho do grupo)